Security
We created various types of network attacks in Internet of Things (IoT) environment for academic purpose. Two typical smart home devices -- SKT NUGU (NU 100) and EZVIZ Wi-Fi Camera (C2C Mini O Plus 1080P) -- were used. All devices, including some laptops or smart phones, were connected to the same wireless network. The dataset consists of 42 raw network packet files (pcap) at different time points.
* The packet files are captured by using monitor mode of wireless network adapter. The wireless headers are removed by Aircrack-ng.
- Categories:
 35005 Views
35005 ViewsThis dataset contains Cyber Threat Intelligence (CTI) data generated from public security reports and malware repositories.
The dataset is stored in a structured format (XML) and includes approximately 640,000 records from 612 security reports published from January 2008 to June 2019.
Several data types are contained in this dataset such as URL, host, IP address, e-mail account, hashes (MD5, SHA1, and SHA256), common vulnerabilities and exposures (CVE), registry, file names ending with specific extensions, and the program database (PDB) path.
- Categories:
 6726 Views
6726 ViewsThis dataset is in support of my 2 research papers - 'Short Circuit Analysis of 72Ah Li-Ion BMC - Part I' and 'Short Circuit Analysis of 72Ah Li-Ion BMC - Part II'.
Faults and datasets can be copied to submit in fire cause investigation reports or thesis.
This dataset is a collection of data of battery and BMC faults.
- Categories:
 5142 Views
5142 ViewsThis dataset is used to design patent. The system is basic , as can be seen from figure.
As the boost converter, BMS is on existing designs.It is very simple for any graduate,degree holder or school students, so no paper is written for it.
There is related dataset-Data: Fifteen 255W Panels Connected Li-Ion
- Categories:
 4617 Views
4617 ViewsThis FFT-75 dataset contains randomly sampled, potentially overlapping file fragments from 75 popular file types (see details below). It is the most diverse and balanced dataset available to the best of our knowledge. The dataset is labeled with class IDs and is ready for training supervised machine learning models. We distinguish 6 different scenarios with different granularity and provide variants with 512 and 4096-byte blocks. In each case, we sampled a balanced dataset and split the data as follows: 80% for training, 10% for testing and 10% for validation.
- Categories:
 2864 Views
2864 Views
Modern technologies have made the capture and sharing of digital video commonplace; the combination of modern smartphones, cloud storage, and social media platforms have enabled video to become a primary source of information for many people and institutions. As a result, it is important to be able to verify the authenticity and source of this information, including identifying the source camera model that captured it. While a variety of forensic techniques have been developed for digital images, less research has been conducted towards the forensic analysis of videos.
- Categories:
 840 Views
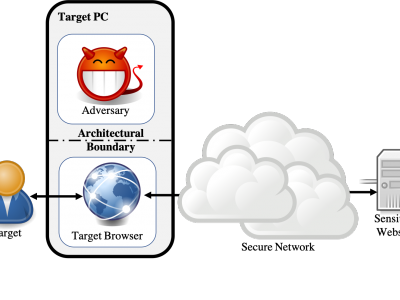
840 ViewsWebsite fingerprinting attacks, which use statistical analysis on network traffic to compromise user privacy, have been shown to be effective even if the traffic is sent over anonymity-preserving networks such as Tor. The classical attack model used to evaluate website fingerprinting attacks assumes an on-path adversary, who can observe all traffic traveling between the user's computer and the secure network.
- Categories:
 957 Views
957 Views